What Technology Provides Secure Access: Best Solutions 2026
Strong authentication, encryption, and Zero Trust design provide secure access anywhere.
If you want to understand What Technology Provides Secure Access across modern apps, clouds, and devices, you are in the right place. I have designed identity systems, rolled out MFA at scale, and led Zero Trust programs. In this guide, I explain What Technology Provides Secure Access, how it works, and how to deploy it with confidence. You will get clear steps, examples, and lessons from the field.

Defining What Technology Provides Secure Access
What Technology Provides Secure Access is the set of tools and methods that let the right user reach the right resource at the right time, and nothing more. It does this through strong identity checks, device health checks, encryption, and real-time policy.
In simple terms, secure access solves three core jobs:
- Prove who you are.
- Check your device and context.
- Shield the path and limit what you can do.
When people ask What Technology Provides Secure Access, they often think of VPNs. Today, the answer is larger. It includes MFA, FIDO2, SSO, ZTNA, SASE, PAM, PKI, and more. These work together to lower risk and raise user trust.
From my own rollouts, the big win comes when identity and network controls act as one. That is where What Technology Provides Secure Access shines: one policy, enforced end to end, with clear logs and proof.

Core Technologies That Provide Secure Access
Below are the main building blocks that answer What Technology Provides Secure Access in real life. Use them in layers for best results.
Strong Authentication (MFA, FIDO2, Biometrics)
- MFA uses two or more factors: something you know, have, or are.
- FIDO2/WebAuthn gives phishing-resistant login with hardware keys or platform authenticators.
- Biometrics help with speed, but pair them with device security.
Lesson learned: Push-based MFA gets phished. FIDO2 keys cut takeovers by a lot in my programs.
Single Sign-On (SSO) and Identity Federation
- SSO reduces password use and login fatigue.
- SAML and OIDC let apps trust your identity provider.
- Conditional access policies gate apps based on risk.
Virtual Private Network (VPN) and Zero Trust Network Access (ZTNA)
- VPN creates an encrypted tunnel to a network.
- ZTNA connects a user to one app, not the whole network.
- ZTNA maps better to cloud and remote work.
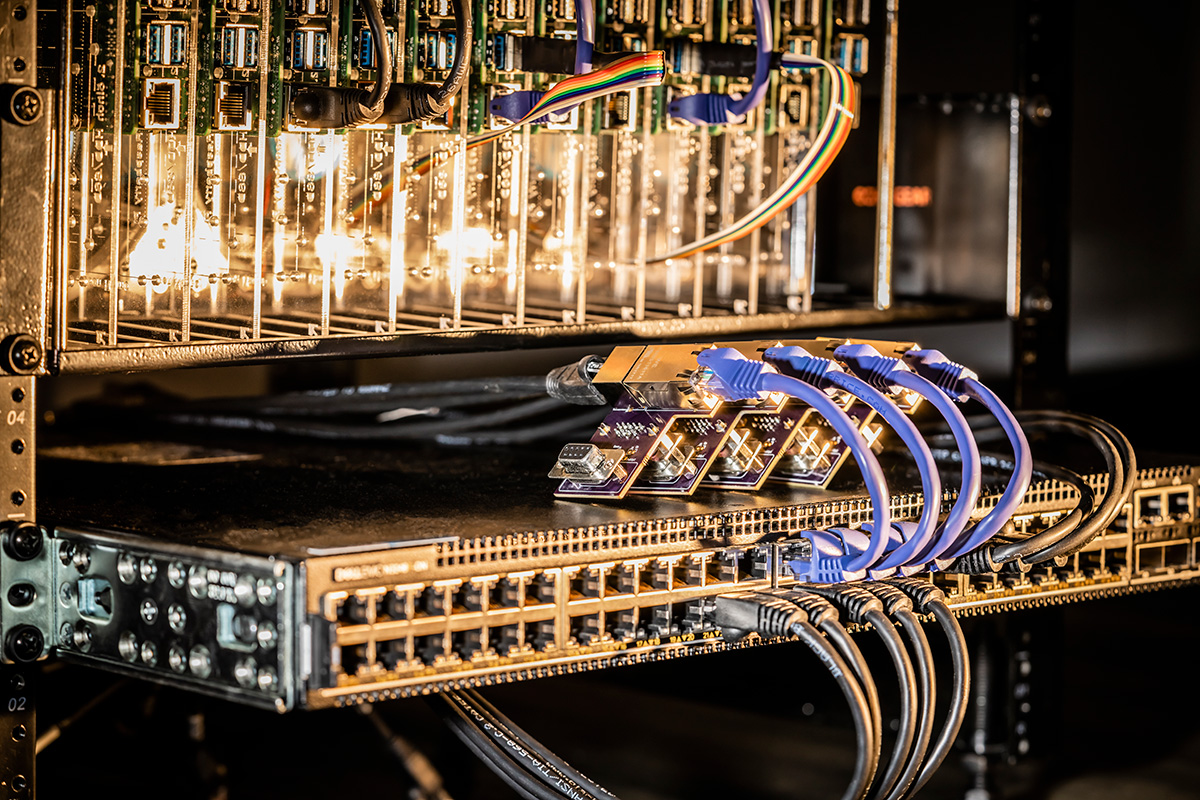
Public Key Infrastructure (PKI) and TLS
- PKI issues and manages certs for users, devices, and services.
- TLS encrypts data in transit and helps stop snooping and tampering.
- Mutual TLS lets both sides prove identity.
Privileged Access Management (PAM)
- Vaults and rotates admin passwords and keys.
- Uses just-in-time access and approvals.
- Records sessions for audit and forensics.
Device and Network Controls (NAC, MDM/UEM, EDR)
- NAC checks device posture before letting it on a network.
- MDM/UEM sets device policies, like disk crypto and patch level.
- EDR detects and stops threats in real time.
Cloud Security Brokers and SASE
- CASB adds policy and data loss control to SaaS apps.
- SASE blends ZTNA, SWG, CASB, and firewall as a cloud edge.
Service Mesh and API Gateways
- Mesh enforces mutual TLS between services and supports fine policy.
- API gateways secure tokens, rate limit, and log calls.
All of these add up to What Technology Provides Secure Access in a full stack. Pick what fits your risk, budget, and roadmap.

How Secure Access Works: From Login to Data
The path from user to data follows a clear flow. What Technology Provides Secure Access ties each step with strong checks and logs.
- Identity proofing. Enroll users with verified identity and assign roles.
- Authentication. Use phishing-resistant MFA or FIDO2.
- Device trust. Check OS, patches, EDR, and encryption.
- Context checks. Look at location, time, app, and behavior risk.
- Authorization. Grant least privilege with role and attribute-based rules.
- Encryption. Enforce TLS and, where needed, mutual TLS.
- Segmentation. Expose only the app, not the network.
- Data controls. Use DLP, tokenization, and rights management.
- Monitoring. Stream logs to SIEM, UEBA, and SOAR for action.
- Review. Re-certify access on a set cadence.
In my teams, tying step 2 and step 3 (user plus device) dropped incident rates fast. It also made audits smooth, since we could show clear, end-to-end proof.
Architectures and Models You Can Trust
Understanding models helps answer What Technology Provides Secure Access at scale.
Zero Trust
- Never trust, always verify, for every request.
- Enforce least privilege and micro-segmentation.
- Assume breach and design for quick detect and contain.
Secure Access Service Edge (SASE)
- Moves network and security to the cloud edge.
- Gives one policy for users anywhere and any device.
- Cuts backhaul costs and reduces latency.
Software-Defined Perimeter (SDP)
- Hides apps from the internet until users pass checks.
- Creates one-to-one, encrypted connections.
- Works well with ZTNA.
These models are not products. They are ways to align tools and policy so What Technology Provides Secure Access stays strong as you grow.

Implementation Roadmap and Best Practices
A clear path beats a big bang. Here is a plan I use when teams ask how to build What Technology Provides Secure Access.
- Map assets and users. Know your apps, data, and user groups.
- Fix identity first. Centralize to one IdP and enable MFA.
- Secure devices. Enforce MDM/UEM, EDR, and disk crypto.
- Start ZTNA for high-risk apps. Migrate off broad VPN access.
- Add PAM for admins. Use just-in-time access.
- Roll out SSO and conditional access rules.
- Protect data. Turn on DLP and logging for SaaS and email.
- Train users. Show how to use keys and report phish.
- Measure and improve. Track login risk, blocks, and time to resolve.
Common mistakes to avoid:
- Trusting push MFA alone. Move to FIDO2 or number-matching.
- Skipping device checks. Compromised devices bypass good passwords.
- Ignoring logs. You cannot prove control without them.
From my field work, pilots beat theory. Start with one app and one user group. Prove value, then scale. This is how What Technology Provides Secure Access becomes a habit, not a project.
Benefits, Trade-offs, and Limitations
What Technology Provides Secure Access brings clear gains, with some trade-offs to plan for.
Benefits
- Lower account takeovers and ransomware risk.
- Faster user access with SSO and smart policy.
- Better audits with unified logs and reports.
Trade-offs
- More tools to run and integrate.
- Change management for users and admins.
- Legacy apps may need refactor or brokers.
Limits and risks
- MFA fatigue and social engineering still occur.
- Device checks can miss zero-days.
- Misconfigurations can expose data even with strong tech.
Be open about these limits. Add compensating controls and monitor often.

Compliance, Standards, and Proof
Regulations and standards guide What Technology Provides Secure Access and help you show due care.
- NIST SP 800-63 for identity assurance and MFA strength.
- FIPS 140-3 for crypto module validation.
- ISO/IEC 27001 for security management systems.
- SOC 2 for service controls and trust.
- HIPAA, PCI DSS, and GDPR for sector and privacy needs.
Use evidence that auditors expect:
- Access reviews, role definitions, and approvals.
- Control screenshots, policies, and change records.
- Log samples from IdP, ZTNA, PAM, and EDR.
Strong controls, backed by proof, build trust with leaders and customers.

Security Metrics That Show Progress
Measure results so you can improve What Technology Provides Secure Access over time.
Key metrics
- MFA adoption rate and percent of phishing-resistant factors.
- Percent of managed devices with required posture.
- Blocked risky logins and false acceptance rate.
- Mean time to detect and respond to access alerts.
- Privileged access request volume and approval latency.
- App exposure: number of apps behind ZTNA vs open network.
Share a short monthly report. Tie numbers to risk reduced and time saved. Leaders fund what they can see.
Frequently Asked Questions of What Technology Provides Secure Access
What Technology Provides Secure Access for remote workers?
Use ZTNA with MFA and device checks. Add SASE for performance and unified policy.
Is VPN still needed if I use ZTNA?
Maybe for a few legacy apps or admin use. Over time, shift most users to ZTNA for least privilege.
Which MFA method is best?
FIDO2 security keys offer strong, phishing-resistant login. If that is not ready, use number-matching push with device checks.
How does SSO impact security?
SSO lowers password reuse and user friction. Pair it with conditional access, and risk goes down while speed goes up.
What Technology Provides Secure Access in a hybrid cloud?
Identity-first controls with MFA, SSO, and ZTNA across on-prem and cloud. Add CASB and PAM, and enforce TLS everywhere.
How do I protect admins and service accounts?
Enable PAM, hardware-backed MFA, and just-in-time access. Rotate secrets and log all privileged sessions.
Can small businesses afford this?
Yes, start with your IdP, MFA, and basic device management. Many vendors bundle ZTNA and SASE at entry tiers.
Conclusion
Secure access is simple in goal and careful in craft. Build on identity, verify device health, encrypt the path, and grant only what is needed. When you combine these steps, What Technology Provides Secure Access becomes a clear program with fast wins.
Take one action this week: enable phishing-resistant MFA for a high-risk app and add a device check. Want deeper help on What Technology Provides Secure Access? Subscribe for new guides, request a checklist, or leave a question so we can solve it together.